Cybersecurity researchers have warned of a malicious marketing campaign focusing on customers of the Python Package deal Index (PyPI) repository with bogus libraries masquerading as “time” associated utilities, however harboring hidden performance to steal delicate knowledge reminiscent of cloud entry tokens.
Software program provide chain safety agency ReversingLabs said it found two units of packages totaling 20 of them. The packages have been cumulatively downloaded over 14,100 occasions –
- snapshot-photo (2,448 downloads)
- time-check-server (316 downloads)
- time-check-server-get (178 downloads)
- time-server-analysis (144 downloads)
- time-server-analyzer (74 downloads)
- time-server-test (155 downloads)
- time-service-checker (151 downloads)
- aclient-sdk (120 downloads)
- acloud-client (5,496 downloads)
- acloud-clients (198 downloads)
- acloud-client-uses (294 downloads)
- alicloud-client (622 downloads)
- alicloud-client-sdk (206 downloads)
- amzclients-sdk (100 downloads)
- awscloud-clients-core (206 downloads)
- credential-python-sdk (1,155 downloads)
- enumer-iam (1,254 downloads)
- tclients-sdk (173 downloads)
- tcloud-python-sdks (98 downloads)
- tcloud-python-test (793 downloads)
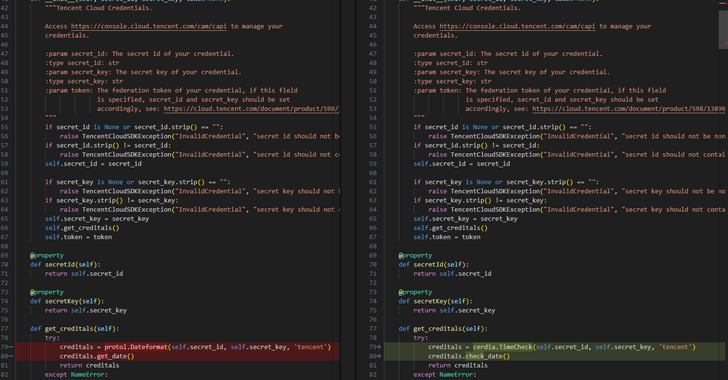
Whereas the primary set pertains to packages which might be used to add knowledge to the risk actor’s infrastructure, the second cluster consists of packages implementing cloud shopper functionalities for a number of companies like Alibaba Cloud, Amazon Net Companies, and Tencent Cloud.
However they’ve additionally been utilizing “time” associated packages to exfiltrate cloud secrets and techniques. All of the recognized packages have already been faraway from PyPI as of writing.
Additional evaluation has revealed that three of the packages, acloud-client, enumer-iam, and tcloud-python-test, has been listed as dependencies of a comparatively common GitHub mission named accesskey_tools that has been forked 42 occasions and began 519 occasions.
A supply code commit referencing tcloud-python-test was made on November 8, 2023, indicating that the package deal has been out there for obtain on PyPI since then. The package deal has been downloaded 793 occasions to this point, per statistics from pepy.tech.
The disclosure comes as Fortinet FortiGuard Labs stated it found 1000’s of packages throughout PyPI and npm, a few of which have been discovered to embed suspicious set up scripts designed to deploy malicious code throughout set up or talk with exterior servers.
“Suspicious URLs are a key indicator of doubtless malicious packages, as they’re usually used to obtain further payloads or set up communication with command-and-control (C&C) servers, giving attackers management over contaminated techniques,” Jenna Wang said.
“In 974 packages, such URLs are linked to the chance of information exfiltration, additional malware downloads, and different malicious actions. It’s essential to scrutinize and monitor exterior URLs in package deal dependencies to stop exploitation.”
Source link