One of many largest sources of confusion within the query of blockchain safety is the exact impact of the block time. If one blockchain has a block time of 10 minutes, and the opposite has an estimated block time of 17 seconds, then what precisely does that imply? What’s the equal of six confirmations on the 10-minute blockchain on the 17-second blockchain? Is blockchain safety merely a matter of time, is it a matter of blocks, or a mix of each? What safety properties do extra complicated schemes have?
Notice: this text won’t go into depth on the centralization dangers related to quick block instances; centralization dangers are a significant concern, and are the first motive to not push block instances all the way in which right down to 1 second regardless of the advantages, and are mentioned at rather more size in this previous article; the aim of this text is to clarify why quick block instances are fascinating in any respect.
The reply the truth is relies upon crucially on the safety mannequin that we’re utilizing; that’s, what are the properties of the attackers that we’re assuming exist? Are they rational, byzantine, economically bounded, computationally bounded, in a position to bribe peculiar customers or not? On the whole, blockchain safety evaluation makes use of certainly one of three totally different safety fashions:
- Regular-case mannequin: there are not any attackers. Both everyone seems to be altruistic, or everyone seems to be rational however acts in an uncoordinated method.
- Byzantine fault tolerance mannequin: a sure share of all miners are attackers, and the remainder are sincere altruistic individuals.
- Financial mannequin: there may be an attacker with a price range of $X which the attacker can spend to both buy their very own {hardware} or bribe different customers, who’re rational.
Actuality is a combination between the three; nevertheless, we are able to glean many insights by inspecting the three fashions individually and seeing what occurs in every one.
The Regular Case
Allow us to first begin off by wanting on the regular case. Right here, there are not any attackers, and all miners merely need to fortunately sing collectively and get alongside whereas they proceed progressively extending the blockchain. Now, the query we need to reply is that this: suppose that somebody despatched a transaction, and okay seconds have elapsed. Then, this individual sends a double-spend transaction making an attempt to revert their authentic transaction (eg. if the unique transaction despatched $50000 to you, the double-spend spends the identical $50000 however directs it into one other account owned by the attacker). What’s the chance that the unique transaction, and never the double-spend, will find yourself within the ultimate blockchain?
Notice that, if all miners are genuinely good and altruistic, they won’t settle for any double-spends that come after the unique transaction, and so the chance ought to strategy 100% after a couple of seconds, no matter block time. One strategy to calm down the mannequin is to imagine a small share of attackers; if the block time is extraordinarily lengthy, then the chance {that a} transaction will probably be finalized can by no means exceed 1-x, the place x is the share of attackers, earlier than a block will get created. We’ll cowl this within the subsequent part. One other strategy is to calm down the altruism assumption and as an alternative focus on uncoordinated rationality; on this case, an attacker making an attempt to double-spend can bribe miners to incorporate their double-spend transaction by putting a better price on it (that is basically Peter Todd’s replace-by-fee). Therefore, as soon as the attacker broadcasts their double-spend, it will likely be accepted in any newly created block, aside from blocks in chains the place the unique transaction was already included.
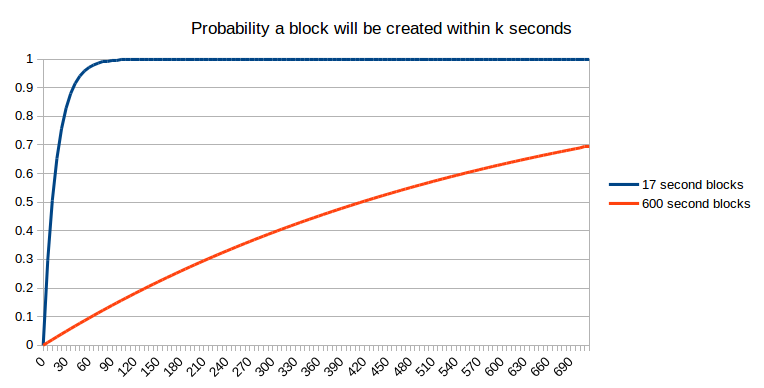
We will incorporate this assumption into our query by making it barely extra complicated: what’s the chance that the unique transaction has been positioned in a block that may find yourself as a part of the ultimate blockchain? Step one to attending to that state is getting included in a block within the first place. The chance that this may happen after okay seconds is fairly effectively established:
Sadly, moving into one block shouldn’t be the top of the story. Maybe, when that block is created, one other block is created on the similar time (or, extra exactly, inside community latency); at that time, we are able to assume as a primary approximation that it’s a 50:50 probability which of these two blocks the following block will probably be constructed on, and that block will in the end “win” – or, maybe, two blocks will probably be created as soon as once more on the similar time, and the competition will repeat itself. Even after two blocks have been created, it is attainable that some miner has not but seen each blocks, and that miner will get fortunate and created three blocks one after the opposite. The probabilities are probably mathematically intractable, so we are going to simply take the lazy shortcut and simulate them:
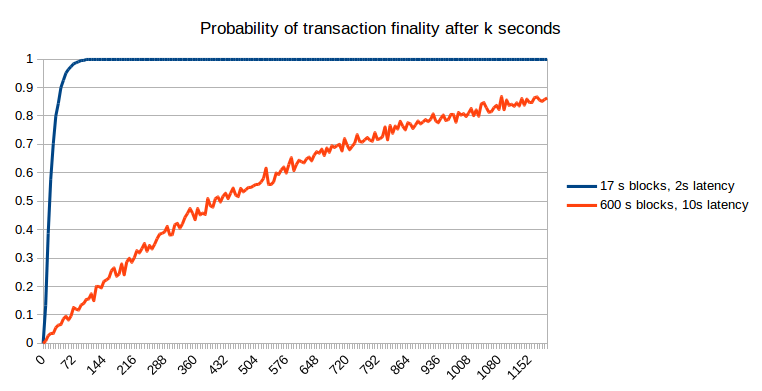
The outcomes may be understood mathematically. At 17 seconds (ie. 100% of the block time), the sooner blockchain offers a chance of ~0.56: barely smaller than the matheatically predicted 1-1/e ~= 0.632 due to the potential of two blocks being created on the similar time and one being discarded; at 600 seconds, the slower blockchain offers a chance of 0.629, solely barely smaller than the anticipated 0.632 as a result of with 10-minute blocks the chance of two blocks being created on the similar time could be very small. Therefore, we are able to see that sooner blockchains do have a slight drawback due to the upper affect of community latency, but when we do a good comparability (ie. ready a selected variety of seconds), the chance of non-reversion of the unique transaction on the sooner blockchain is way higher.
Attackers
Now, let’s add some attackers into the image. Suppose that portion X of the community is taken up by attackers, and the remaining 1-X is made up of both altruistic or egocentric however uncoordinated (barring egocentric mining issues, as much as X it truly doesn’t matter which) miners. The only mathematical mannequin to make use of to approximate that is the weighted random stroll. We begin off assuming {that a} transaction has been confirmed for okay blocks, and that the attacker, who can also be a miner, now tries to start out a fork of the blockchain. From there, we characterize the scenario with a rating of okay, which means that the attacker’s blockchain is okay blocks behind the unique chain, and at each step make the commentary that there’s a chance of X that the attacker will make the following block, altering the rating to k-1 and a chance of 1-X that sincere miners mining on the unique chain will make the following block, altering the rating to okay+1. If we get to okay = 0, that signifies that the unique chain and the attacker’s chain have the identical size, and so the attacker wins.
Mathematically, we all know that the chance of the attacker successful such a recreation (assuming x as in any other case the attacker can overwhelm the community it doesn’t matter what the blockchain parameters are) is:
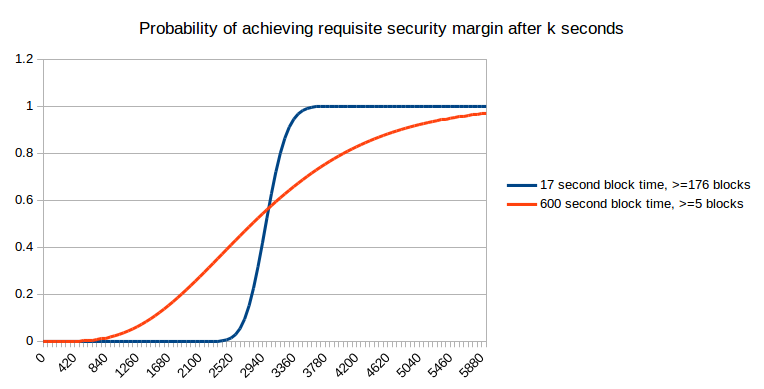
We will mix this with a chance estimate for okay (utilizing the Poisson distribution) and get the online chance of the attacker successful after a given variety of seconds:
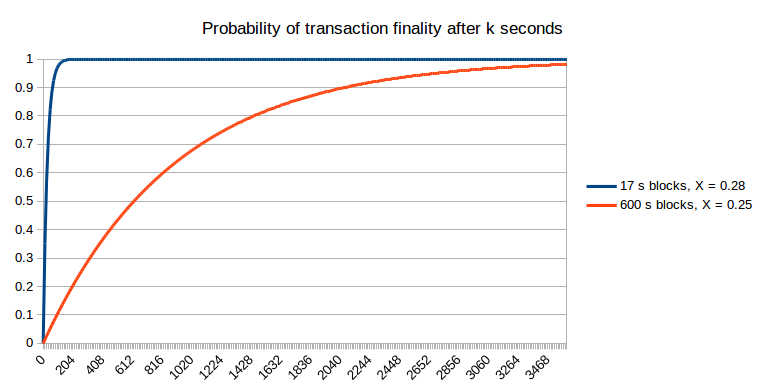
Notice that for quick block instances, we do need to make an adjustment as a result of the stale charges are increased, and we do that within the above graph: we set X = 0.25 for the 600s blockchain and X = 0.28 for the 17s blockchain. Therefore, the sooner blockchain does permit the chance of non-reversion to achieve 1 a lot sooner. One different argument that could be raised is that the lowered value of attacking a blockchain for a brief period of time over an extended period of time signifies that assaults towards quick blockchains might occur extra regularly; nevertheless, this solely barely mitigates quick blockchains’ benefit. For instance, if assaults occur 10x extra usually, then which means we should be comfy with, for instance, a 99.99% chance of non-reversion, if earlier than we had been comfy with a 99.9% chance of non-reversion. Nevertheless, the chance of non-reversion approaches 1 exponentially, and so solely a small variety of additional confirmations (to be exact, round two to 5) on the sooner chain is required to bridge the hole; therefore, the 17-second blockchain will probably require ten confirmations (~three minutes) to realize the same diploma of safety underneath this probabilistic mannequin to 6 confirmations (~one hour) on the ten-minute blockchain.
Economically Bounded Attackers
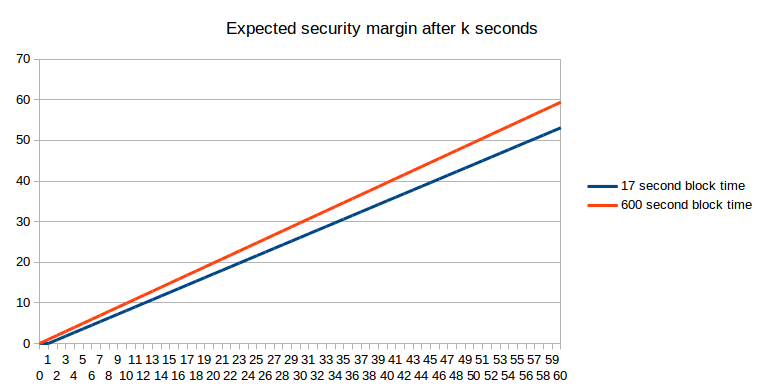
We will additionally strategy the topic of attackers from the opposite aspect: the attacker has $X to spend, and might spend it on bribes, near-infinite instantaneous hashpower, or anything. How excessive is the requisite X to revert a transaction after okay seconds? Primarily, this query is equal to “how a lot financial expenditure does it take to revert the variety of blocks that may have been produced on high of a transaction after okay seconds”. From an expected-value standpoint, the reply is straightforward (assuming a block reward of 1 coin per second in each instances):
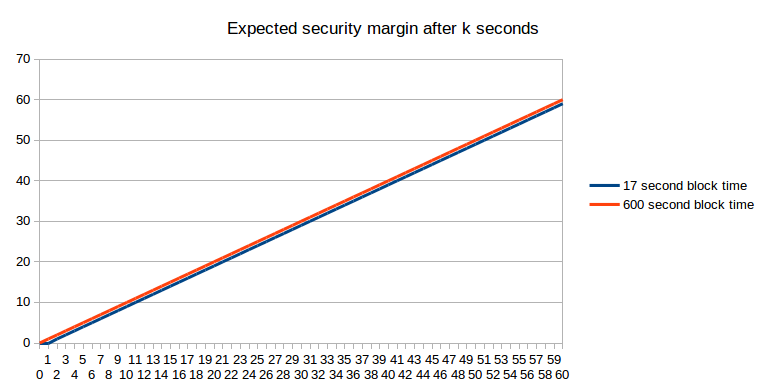
If we have in mind stale charges, the image truly turns barely in favor of the longer block time:
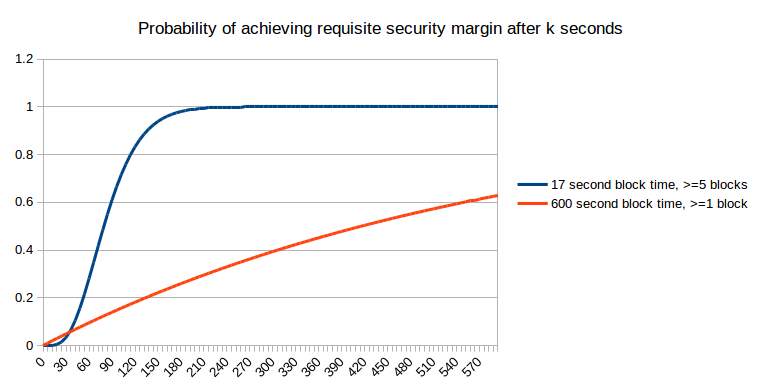
However “what’s the anticipated financial safety margin after okay seconds” (utilizing “anticipated” right here within the formal probability-theoretic sense the place it roughly means “common”) is definitely not the query that most individuals are asking. As an alternative, the issue that considerations peculiar customers is arguably certainly one of them desirous to get “sufficient” safety margin, and desirous to get there as shortly as attainable. For instance, if I’m utilizing the blockchain to buy a $2 espresso, then a safety margin of $0.03 (the present bitcoin transaction price, which an attacker would wish to outbid in a replace-by-fee mannequin) is clearly not sufficient, however a safety margin of $5 is clearly sufficient (ie. only a few assaults would occur that spend $5 to steal $2 from you), and a safety margin of $50000 shouldn’t be a lot better. Now, allow us to take this strict binary sufficient/not-enough mannequin and apply it to a case the place the cost is so small that one block reward on the sooner blockchain is bigger than the associated fee. The chance that we’ll have “sufficient” safety margin after a given variety of seconds is strictly equal to a chart that we already noticed earlier:
Now, allow us to suppose that the specified safety margin is price between 4 and 5 instances the smaller block reward; right here, on the smaller chain we have to compute the chance that after okay seconds a minimum of 5 blocks can have been produced, which we are able to do through the Poisson distribution:
Now, allow us to suppose that the specified safety margin is price as a lot because the bigger block reward:
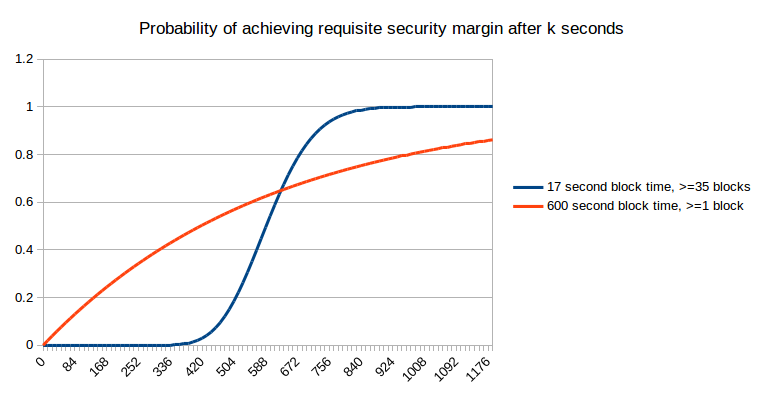
Right here, we are able to see that quick blocks not present an unambiguous profit; within the quick time period they really damage your probabilities of getting extra safety, although that’s compensated by higher efficiency in the long run. Nevertheless, what they do present is extra predictability; quite than an extended exponential curve of attainable instances at which you’ll get sufficient safety, with quick blocks it’s just about sure that you’ll get what you want inside 7 to 14 minutes. Now, allow us to preserve growing the specified safety margin additional:
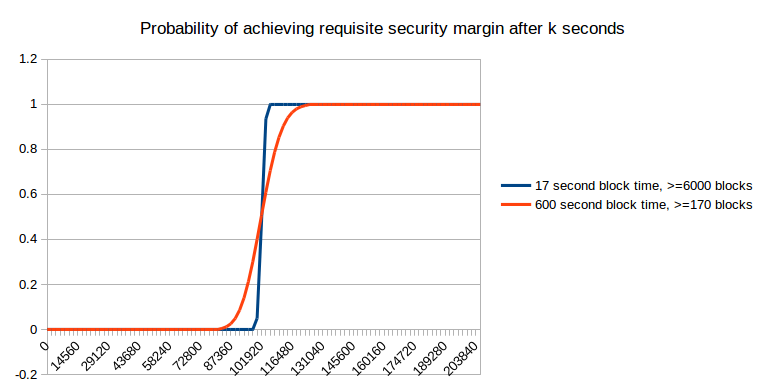
As you may see, as the specified safety margin will get very excessive, it not actually issues that a lot. Nevertheless, at these ranges, it’s important to wait a day for the specified safety margin to be achieved in any case, and that may be a size of time that almost all blockchain customers in apply don’t find yourself ready; therefore, we are able to conclude that both (i) the financial mannequin of safety shouldn’t be the one that’s dominant, a minimum of on the margin, or (ii) most transactions are small to medium sized, and so truly do profit from the higher predictability of small block instances.
We also needs to point out the potential of reverts on account of unexpected exigencies; for instance, a blockchain fork. Nevertheless, in these instances too, the “six confirmations” utilized by most websites shouldn’t be sufficient, and ready a day is required with the intention to be really protected.
The conclusion of all that is easy: sooner block instances are good as a result of they supply extra granularity of data. Within the BFT safety fashions, this granularity ensures that the system can extra shortly converge on the “right” fork over an incorrect fork, and in an financial safety mannequin which means the system can extra shortly give notification to customers of when a suitable safety margin has been reached.
In fact, sooner block instances do have their prices; stale charges are maybe the biggest, and it’s after all essential to stability the 2 – a stability which would require ongoing analysis, and even perhaps novel approaches to fixing centralization issues arising from networking lag. Some builders might have the opinion that the consumer comfort supplied by sooner block instances shouldn’t be definitely worth the dangers to centralization, and the purpose at which this turns into an issue differs for various individuals, and may be pushed nearer towards zero by introducing novel mechanisms. What I’m hoping to disprove right here is solely the declare, repeated by some, that quick block instances present no profit by any means as a result of if every block is fifty instances sooner then every block is fifty instances much less safe.
Appendix: Eyal and Sirer’s Bitcoin NG
A latest fascinating proposal offered on the Scaling Bitcoin convention in Montreal is the concept of splitting blocks into two varieties: (i) rare (eg. 10 minute heartbeat) “key blocks” which choose the “chief” that creates the following blocks that include transactions, and (ii) frequent (eg. 10 second heartbeat) “microblocks” which include transactions:
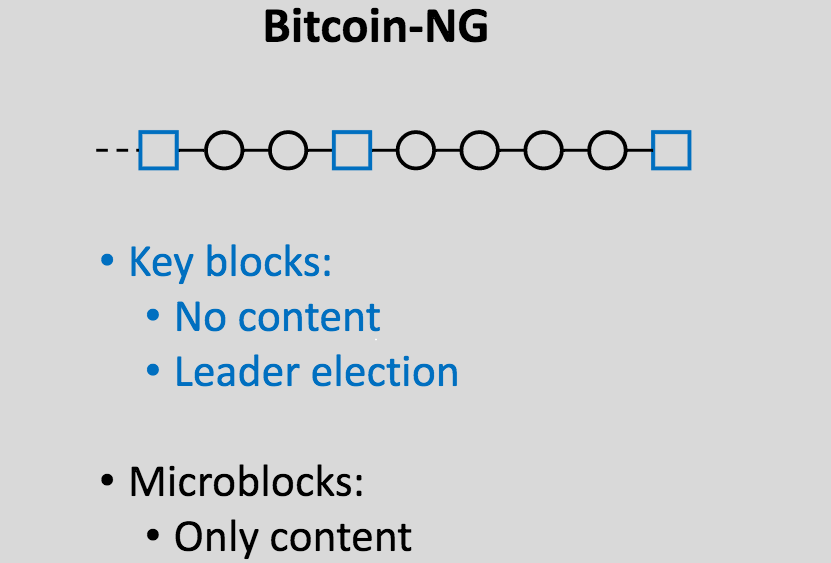
The idea is that we are able to get very quick blocks with out the centralization risks by basically electing a dictator solely as soon as each (on common) ten minutes, for these ten minutes, and permitting the dictator to provide blocks in a short time. A dictator “ought to” produce blocks as soon as each ten seconds, and within the case that the dictator makes an attempt to double-spend their very own blocks and create an extended new set of microblocks, a Slasher-style algorithm is used the place the dictator may be punished in the event that they get caught:
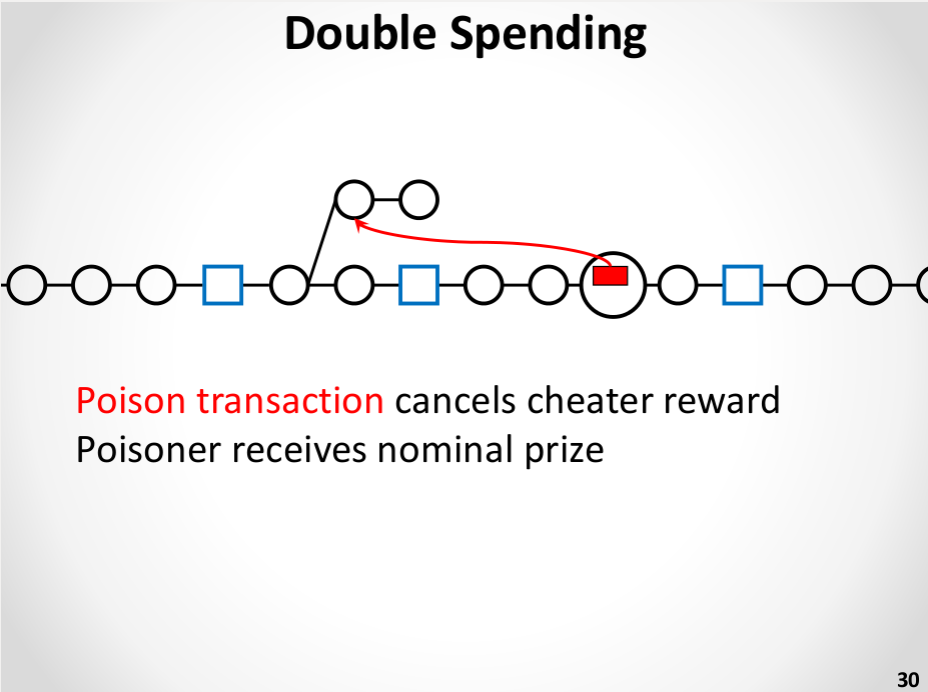
That is definitely an enchancment over plain previous ten-minute blocks. Nevertheless, it’s not almost as efficient as merely having common blocks come as soon as each ten seconds. The reasoning is straightforward. Below the economically-bounded attacker mannequin, it truly does provide the identical possibilities of assurances because the ten-second mannequin. Below the BFT mannequin, nevertheless, it fails: if an attacker has 10% hashpower then the chance {that a} transaction will probably be ultimate can’t exceed 90% till a minimum of two key blocks are created. In actuality, which may be modeled as a hybrid between the financial and BFT situations, we are able to say that despite the fact that 10-second microblocks and 10-second actual blocks have the identical safety margin, within the 10-second microblock case “collusion” is less complicated as inside the 10-minute margin just one social gathering must take part within the assault. One attainable enchancment to the algorithm could also be to have microblock creators rotate throughout every inter-key-block part, taking from the creators of the final 100 key blocks, however taking this strategy to its logical conclusion will probably result in reinventing full-on Slasher-style proof of stake, albeit with a proof of labor issuance mannequin connected.
Nevertheless, the final strategy of segregating chief election and transaction processing does have one main profit: it reduces centralization dangers on account of gradual block propagation (as key block propagation time doesn’t rely on the scale of the content-carrying block), and thus considerably will increase the utmost protected transaction throughput (even past the margin supplied by means of Ethereum-esque uncle mechanisms), and for that reason additional analysis on such schemes ought to definitely be carried out.
Source link

