The U.S. Division of Justice (DoJ) has introduced fees towards 12 Chinese language nationals for his or her alleged participation in a wide-ranging scheme designed to steal information and suppress free speech and dissent globally.
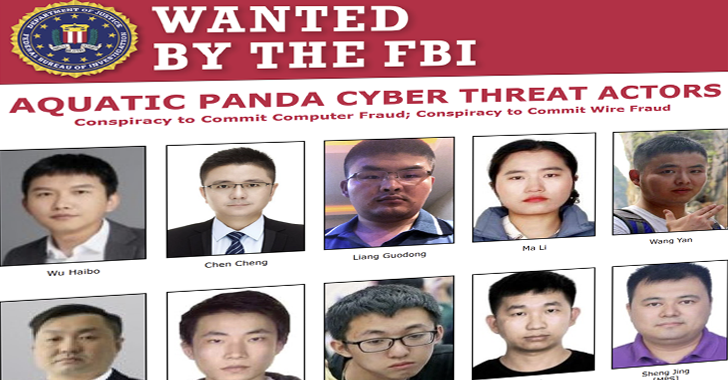
The individuals embody two officers of the Individuals’s Republic of China’s (PRC) Ministry of Public Safety (MPS), eight workers of an ostensibly personal PRC firm, Anxun Data Expertise Co. Ltd. (安洵信息技术有限公司) also called i-Soon, and members of Superior Persistent Risk 27 (APT27, aka Budworm, Bronze Union, Emissary Panda, Fortunate Mouse, and Iron Tiger) –
- Wu Haibo (吴海波), Chief Government Officer
- Chen Cheng (陈诚), Chief Working Officer
- Wang Zhe (王哲), Gross sales Director
- Liang Guodong (梁国栋), Technical Employees
- Ma Li (马丽), Technical Employees
- Wang Yan (王堰), Technical Employees
- Xu Liang (徐梁), Technical Employees
- Zhou Weiwei (周伟伟), Technical Employees
- Wang Liyu (王立宇), MPS Officer
- Sheng Jing (盛晶), MPS Officer
- Yin Kecheng (尹可成), APT27 actor aka “YKC”
- Zhou Shuai (周帅), APT27 actor aka “Coldface”
“These malicious cyber actors, appearing as freelancers or as workers of i-Quickly, performed pc intrusions on the path of the PRC’s MPS and Ministry of State Safety (MSS) and on their very own initiative,” the DoJ said. “The MPS and MSS paid handsomely for stolen information.”
Court docket paperwork reveal that the MPS and MSS employed a community of personal corporations and contractors in China to indiscriminately infiltrate corporations and steal information, whereas additionally obscuring the involvement of the federal government.
The eight i-Quickly workers, alongside two MPS officers, have been accused of breaking into e-mail accounts, cell telephones, servers, and web sites from at the very least in or round 2016 by in or round 2023.
The U.S. Federal Bureau of Investigation (FBI), in a courtroom submitting, mentioned the actions related to i-Quickly are tracked by the cybersecurity group underneath the monikers Aquatic Panda (aka RedHotel), whereas APT27 overlaps with that of Silk Typhoon, UNC5221, and UTA0178.
The company additional pointed out that the Chinese language authorities is utilizing formal and casual connections with freelance hackers and data safety corporations to compromise pc networks worldwide.
Individually, the U.S. Division of State’s Rewards for Justice (RFJ) program has announced a reward of as much as $10 million for data resulting in the identification or location of any one who engages in malicious cyber actions towards U.S. important infrastructure whereas appearing underneath the path of a international authorities.
The DoJ additional famous that i-Quickly and its workers generated tens of thousands and thousands of {dollars} in income, making the corporate a key participant within the PRC hacker-for-hire ecosystem. It is estimated to have charged wherever between $10,000 and $75,000 for every e-mail inbox it efficiently exploited.
“In some situations, i-Quickly performed pc intrusions on the request of the MSS or MPS, together with cyber-enabled transnational repression on the path of the MPS officer defendants,” the division mentioned.
“In different situations, i-Quickly performed pc intrusions by itself initiative after which offered, or tried to promote, the stolen information to at the very least 43 totally different bureaus of the MSS or MPS in at the very least 31 separate provinces and municipalities in China.”
Targets of i-Quickly’s assaults included a big non secular group in the USA, critics and dissidents of the PRC authorities, a state legislative physique, United States authorities companies, the ministries of international affairs of a number of governments in Asia, and information organizations.
An extra financial reward of as much as $2 million every has been announced for data resulting in the arrests and/or convictions of Shuai and Kecheng, who’re accused of taking part in a years-long, refined pc hacking conspiracies to breach U.S. sufferer corporations, municipalities, and organizations for revenue from 2011, and steal information after establishing persistent entry through the PlugX malware.
Concurrent to the costs, the DoJ has additionally introduced the seizure of 4 domains linked to i-Quickly and the APT27 actors.
- ecoatmosphere.org
- newyorker.cloud
- heidrickjobs.com, and
- maddmail.web site
“i-Quickly’s victims had been of curiosity to the PRC authorities as a result of, amongst different causes, they had been distinguished abroad critics of the PRC authorities or as a result of the PRC authorities thought-about them threatening to the rule of the Chinese language Communist Get together,” the DoJ said.
The corporate can be mentioned to have educated MPS workers the best way to hack independently of i-Quickly and offered on the market numerous hacking strategies that it described as an “industry-leading offensive and defensive expertise” and a “zero-day vulnerability arsenal.”
Marketed among the many instruments was a software program known as the “Automated Penetration Testing Platform” that is able to sending phishing emails, creating recordsdata with malware that present distant entry to victims’ computer systems upon opening, and cloning web sites of victims in an try and trick them into offering delicate data.
One other of i-Quickly’s choices is a password-cracking utility often called the “Divine Mathematician Password Cracking Platform” and a program engineered to hack into numerous on-line providers like Microsoft Outlook, Gmail, and X (previously Twitter), amongst others.
“With respect to Twitter, i-Quickly offered software program with the aptitude to ship a sufferer a spear phishing hyperlink after which to acquire entry to and management over the sufferer’s Twitter account,” the DoJ defined.
“The software program had the flexibility to entry Twitter even with out the sufferer’s password and to bypass multi-factor authentication. After a sufferer’s Twitter was compromised, the software program may ship tweets, delete tweets, ahead tweets, make feedback, and like tweets.”
The aim of the device, known as “Public Opinion Steering and Management Platform (Abroad),” was to let the corporate’s prospects leverage the community of hacked X accounts to know public opinion exterior of China.
“The costs introduced in the present day expose the PRC’s continued makes an attempt to spy on and silence anybody it deems threatening to the Chinese language Communist Get together,” Appearing Assistant Director in Cost Leslie R. Backschies mentioned in an announcement.
“The Chinese language authorities tried to hide its efforts by working by a personal firm, however their actions quantity to years of state-sponsored hacking of spiritual and media organizations, quite a few authorities companies in a number of international locations, and dissidents around the globe who dared criticize the regime.”
Source link